Hackers have [Ep4] Secret Campusdiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 A beginner’s guide to balloon play during sex
A beginner’s guide to balloon play during sex
 Wharton, Borges, and Grey: Fan
Wharton, Borges, and Grey: Fan
 Letter from India: When the Cat’s Away by Amie Barrodale
Letter from India: When the Cat’s Away by Amie Barrodale
 Golden State Warriors vs. Los Angeles Lakers 2025 livestream: Watch NBA online
Golden State Warriors vs. Los Angeles Lakers 2025 livestream: Watch NBA online
 Dear Paris Review, Where Do I Publish? by Lorin Stein
Dear Paris Review, Where Do I Publish? by Lorin Stein
 Memes are the latest love language, Hinge says
Memes are the latest love language, Hinge says
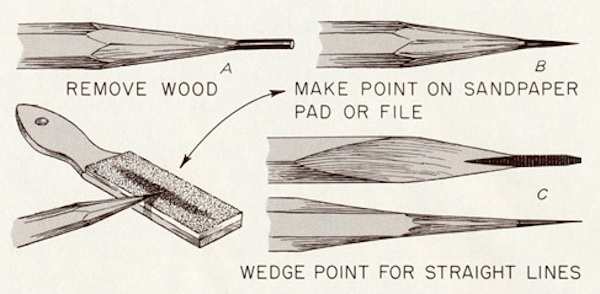 Psychos, Pencils, and Fines by Sadie Stein
Psychos, Pencils, and Fines by Sadie Stein
 Obama photographer Pete Souza on Trump: 'We failed our children'
Obama photographer Pete Souza on Trump: 'We failed our children'
 Wordle today: Here's the answer and hints for May 25
Wordle today: Here's the answer and hints for May 25
 Amazon Kindle Paperwhite Kids: $139.99 at Amazon
Amazon Kindle Paperwhite Kids: $139.99 at Amazon
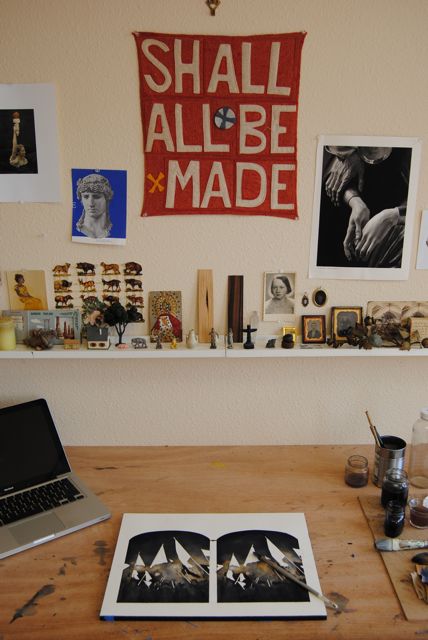 Pirate Queen: In the Studio with June Glasson by Charlotte Strick
Pirate Queen: In the Studio with June Glasson by Charlotte Strick
 Kubrick, Steinbeck, and Stine, Oh My! by Sadie Stein
Kubrick, Steinbeck, and Stine, Oh My! by Sadie Stein
 The Clown Continuum by Monica Drake
The Clown Continuum by Monica Drake
 Amazon Kindle Paperwhite Kids: $139.99 at Amazon
Amazon Kindle Paperwhite Kids: $139.99 at Amazon
 How to watch the 2023 French Open: Use a VPN to stream it live
How to watch the 2023 French Open: Use a VPN to stream it live
 ESPN host breaks into tears while talking about racism in America
ESPN host breaks into tears while talking about racism in America
 'The Princess Bride' cast is reuniting to help Wisconsin Democrats
'The Princess Bride' cast is reuniting to help Wisconsin Democrats
 NYT Connections Sports Edition hints and answers for February 11: Tips to solve Connections #141
NYT Connections Sports Edition hints and answers for February 11: Tips to solve Connections #141
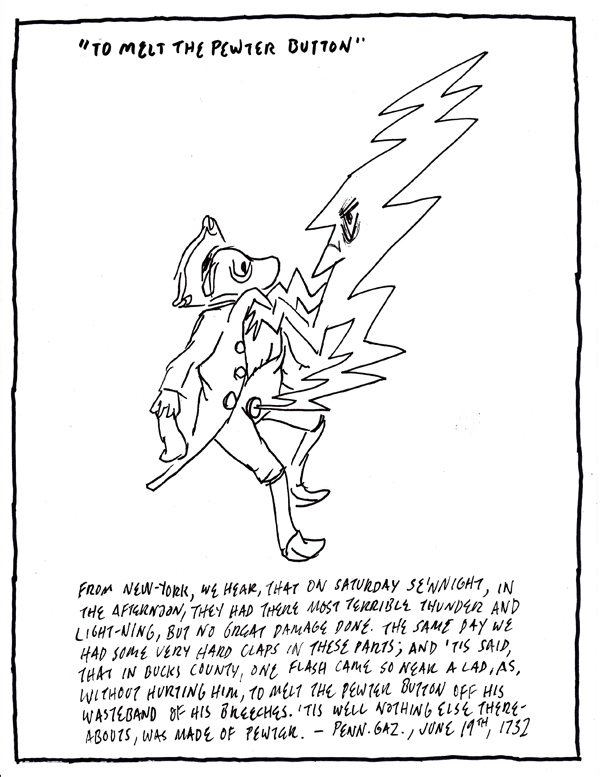 Benjamin Franklin's Clippings, Circa 1730 by Jason Novak
Benjamin Franklin's Clippings, Circa 1730 by Jason Novak
The pet toy massacres of 'Toy Story' must be stoppedHBO Max's 'Fresh Prince' reunion is a blueprint for streaming servicesDonald Trump just retweeted the world's worst eclipse meme, and this can't be realThese weirdDozens of proSenators warn Facebook, Twitter at postA German news magazine just gave us the most shocking Donald Trump cover yetBear enters home and only leaves after getting punched in the faceDHS cybersecurity director subtweets Trump after being fired via tweetEverything coming to Hulu in December 2020We read Obama's 'A Promised Land' so you don't have to, but you should'Star Wars: Tales from the Galaxy’s Edge' VR delivers what Disney’s theme parks can’tHBO reportedly leaving Amazon Prime in 2021 to make way for HBO MaxThe pet toy massacres of 'Toy Story' must be stoppedTeardown of iPhone 12 Pro Max reveals big battery, big camera sensor8 ways climate change is already impacting youSamsung's new Galaxy A12 offers quad camera and massive battery on the cheapThe White House is set to roll out its transgender soldiers banApple promises Xbox Series X controller support on iPhone in updateiFixit teardown confirms Apple's M1 MacBooks are basically the same as their predecessors Hillary Clinton was spotted at a Broadway musical and everyone freaked out Don’t shame people who don’t wear masks. It won't work. Google Maps just made it way easier to rent a bike in 10 cities DeFi could become the next big thing in finance 'Cursed' falls short of fantasy in a waterlogged Season 1: Review Everything coming to Hulu in August 2020 TheirTube shows how YouTube's algorithm creates conspiracy theorists This dead hacker's account could be the key to the big Twitter hack Finally, you can buy this giant Frankenstein of a sex toy Pence adds more pets to the Second Family menagerie Cloudflare goes down, and takes the internet's security blanket with it Snapchat says it is 'actively going after' political ads as revenue Zuckerberg criticizes Trump response to coronavirus in Fauci Q&A Fitbit sponsors Timberwolves, becomes NBA's first official wearable Delivery apps become essential for restaurants to survive during pandemic How the Twitter hack highlights the dangers of Slack How to file for a piece of that $117.5 million Yahoo data Watch Hulu's Freestyle Love Supreme doc, then check out the TV series 'Shadow Warrior 3' developers want players to feel overpowered 5 new Lyft features we are looking forward to
2.252s , 10137.2734375 kb
Copyright © 2025 Powered by 【[Ep4] Secret Campus】,Creation Information Network